The maintenance (MA) domain focuses on the physical and digital upkeep of your systems. Much like a car needs oil changes, your system needs regular care to prevent failures. This domain ensures that only authorized people perform repairs. It ensures that they follow strict rules to protect your sensitive data while they work. The maintenance family requires you to track who touches your equipment and what they do to it. It prevents "secret" changes that could weaken your defenses. Maintenance controls, you focus on authorized repairs, tools and equipment, and remote maintenance. This domain places a heavy focus on maintenance supervision. You should not leave an outside technician alone with sensitive hardware. Supervising work ensures the technician only accesses the system(s) they need to fix.
Domain level policies address the controls implemented within systems and organizations. Policies are the perfect home to define control parameters, such as frequencies. Procedures describe the implementation of policies or controls. Organizations may document procedures within the system security plan or within separate documents. Here are some of the principles that guided this maintenance policy:
A cover page tracks specific details regarding the policy, including:
NIST SP 800-53 defines specific objectives for domain-level policies. From this guidance we incorporate the following major sections into our policy:
The purpose statement should identify why the policy exists and what it aims to achieve.
The scope should identify who it applies to and under what circumstances.
The policy governance section covers most of the organization defined parameters. These subsections cover the following details:
The fourth section includes our policy statements. Subsection headings group related Policy statements together. Each policy statement has a unique number for traceability to other documents. A policy statement number consists of the section, subsection, and policy statement order.
The fifth section identifies the relevant roles and responsibilities identified in the policy. A single, short paragraph describes the responsibilities for each role. The sixth section identifies the supporting procedures. We opted to align our subsection headings with the names of supporting procedures. The seventh section identifies related documents, to include relevant policies. The eighth section documents a revision history. This table captures policy changes, including: version, effective date, approver(s), change summaries. The ninth section captures a formal authorization of the policy by the policy owner.
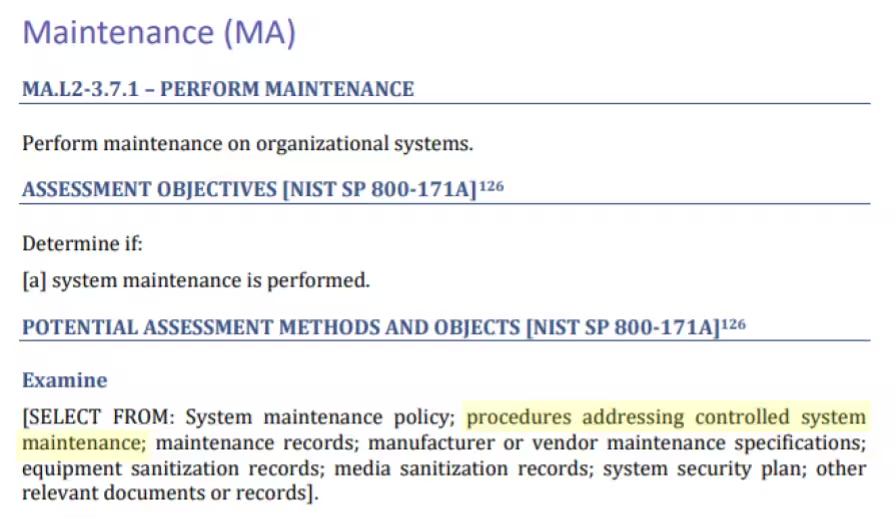
NIST identified a named set of procedures for each practice within NIST SP 800-171. The assessment guide (SP 800-171A) contains the original mappings. The CMMC assessment guides include this mapping as well. The potential assessment methods and objects section contains a subsection called examine. Within each practice, NIST identified relevant policies, procedures and other artifacts. We used the relevant procedures to organize the section headings within each policy.
The organization must vet all support vendors before hiring them for services. Vendors must prove they screen their staff and follow strict government security rules. If a vendor will have access to sensitive data, they must meet high security standards. Staff wipe hardware of all sensitive information before it leaves the organization's control. The team must use government-approved methods to ensure the data is unrecoverable. Staff destroy storage components of broken devices by shredding or crushing.
CMMC Objectives Covered in This Section:
Staff track every tool used for maintenance through official service and change requests. These tools must stay updated and patched like any other company system. Staff inspect third-party provided tools for viruses and verify its digital fingerprint (hash). When downloading software, technicians must scan the files for malicious code before installation. Staff may only download installation files from reputable vendor websites or official resellers.
CMMC Objectives Covered in This Section:
The organization assigns a specific leader to oversee all repair and upkeep activities. This ensures that every fix follows the company’s security rules. Only staff members who already have special "privileged" access can perform maintenance. Internal staff supervise outside technicians at all times. This "shadow" ensures the guest only accesses what is necessary for the job. When possible, internal staff should perform the technical steps using the vendor's instructions.
CMMC Objectives Covered in This Section:
The organization places tight controls on remote repairs. The CISO must approve any remote maintenance connection before it starts. All remote maintenance sessions use multi-factor authentication. For direct connections, staff must use unique credentials and security keys when possible. Internal Staff must observe all remote maintenance sessions. Staff must disable connections immediately upon completion of remote maintenance. Permanent diagnostic links must stay off unless an authorized maintenance window is open.
CMMC Objectives Covered in This Section:
FedRAMP guidance on how to write a control implementation statement states the following:
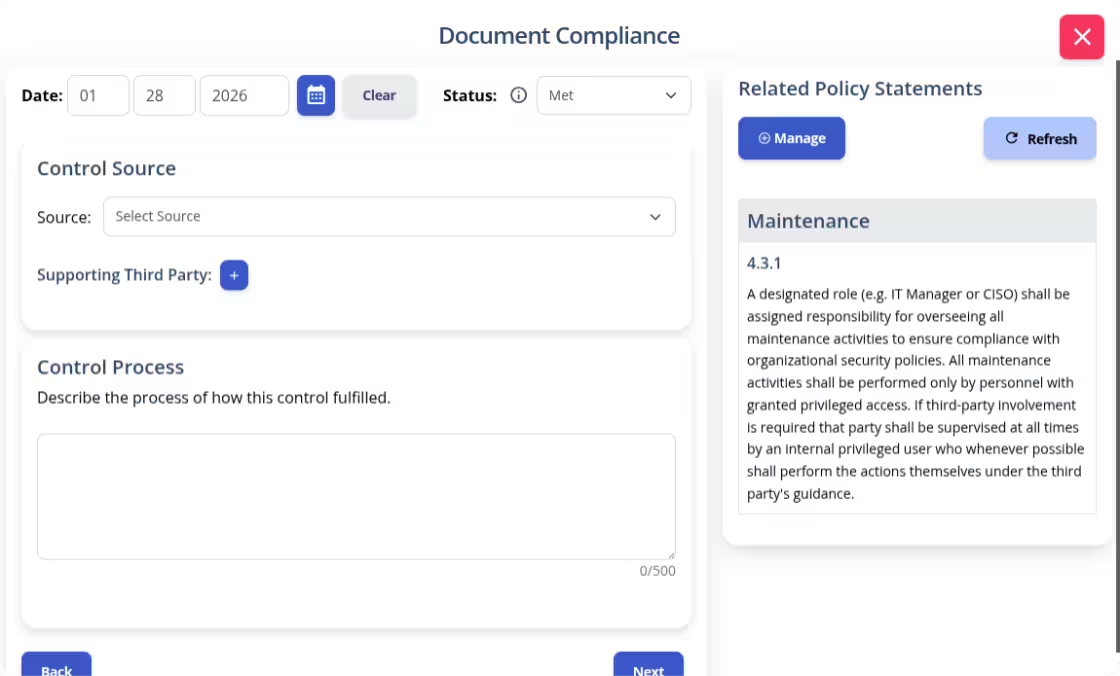
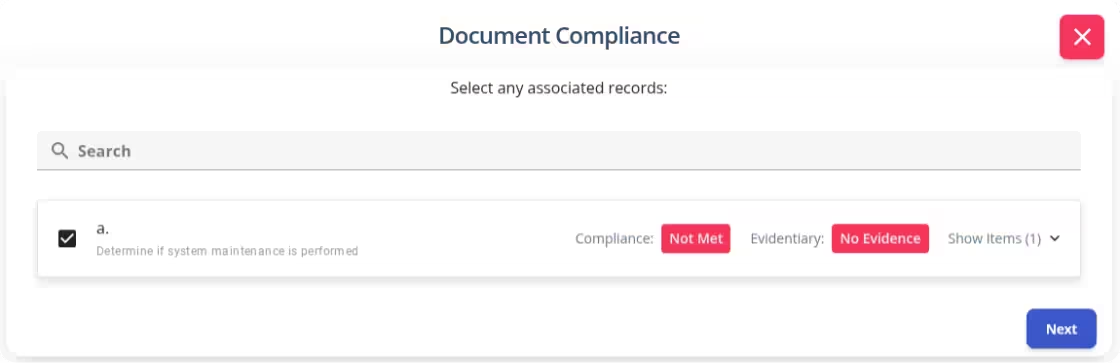
Write your policies before you start drafting your security plan. K2 GRC shows you exactly how each part of your policy connects to your security goals. This starts with selecting an objective to document.
After selecting a criteria, K2 GRC shows policy statements relevant to that criteria. The input screen shows the specific policy name and the statement’s number. This enables users to cite relevant policy sections within the control narratives. The system aggregates these control narratives to populate the system security plan (SSP).
Trusting outsiders with your systems is stressful for business and IT leaders. You’ve worked too hard to build your business to let a simple repair session turn into a security nightmare. Without a clear plan, you are leaving your most sensitive data to chance. A strong Maintenance policy takes the guesswork out of the equation. It replaces that nagging worry with the confidence that comes from total oversight. When you have a formal process in place, you are no longer hoping for the best. You ensure it by vetting and supervising vendors.
It turns a risky necessity into a routine, secure operation. Don't wait for a maintenance mishap to realize your policy is missing. Download our Maintenance Policy template today to get the professional foundation you need. Give your team guidance to handle repairs with precision and regulatory conformance.