The Incident Response (IR) domain focuses on how your organization handles a "bad day." Even with the best defenses, security breaches can still happen. This domain ensures that when a problem occurs, you know how to detect it, stop it, and get your systems back to work. The IR family moves your organization from being reactive to prepared. It requires you to create a formal plan so that no one has to guess what to do during a crisis. IR controls focus on four main stages: preparation, detection, containment, and recovery.
A plan that sits on a shelf is not helpful. This domain emphasizes Incident Response Testing. You must run "tabletop exercises" where your leaders walk through a test disaster. This practice builds "muscle memory" so your team stays calm when a real emergency hits. Having a solid IR process stops attacks early and gets your systems running again faster. Incident Response turns a potential catastrophe into a manageable event. It ensures that a single mistake or attack does not put you out of business.
Domain level policies address the controls implemented within systems and organizations. Policies are the perfect home to define control parameters, such as frequencies. Procedures describe the implementation of policies or controls. Organizations may document procedures within the system security plan or within separate documents. Here are some of the principles that guided this incident response policy:
A cover page tracks specific details regarding the policy, including:
NIST SP 800-53 defines specific objectives for domain-level policies. From this guidance we incorporate the following major sections into our policy:
The purpose statement should identify why the policy exists and what it aims to achieve.
The scope should identify who it applies to and under what circumstances.
The policy governance section covers most of the organization defined parameters. These subsections cover the following details:
The fourth section includes our policy statements. Subsection headings group related Policy statements together. Each policy statement has a unique number for traceability to other documents. A policy statement number consists of the section, subsection, and policy statement order.
The fifth section identifies the relevant roles and responsibilities identified in the policy. A single, short paragraph describes the responsibilities for each role. The sixth section identifies the supporting procedures. We opted to align our subsection headings with the names of supporting procedures. The seventh section identifies related documents, to include relevant policies. The eighth section documents a revision history. This table captures policy changes, including: version, effective date, approver(s), change summaries. The ninth section captures a formal authorization of the policy by the policy owner.
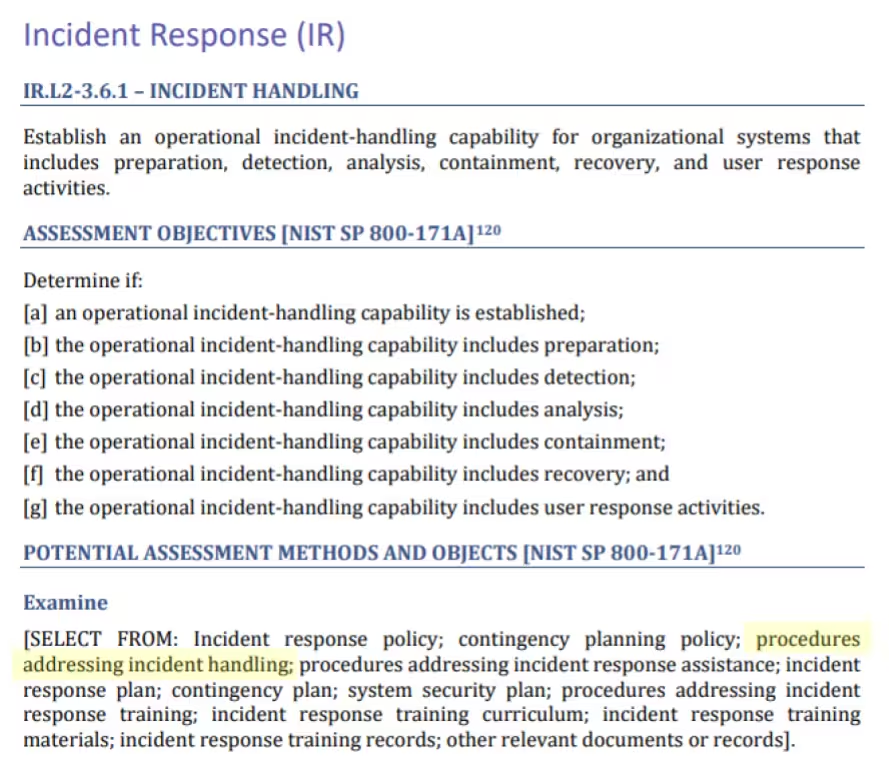
NIST identified a named set of procedures for each practice within NIST SP 800-171. The assessment guide (SP 800-171A) contains the original mappings. The CMMC assessment guides include this mapping as well. The potential assessment methods and objects section contains a subsection called examine. Within each practice, NIST identified relevant policies, procedures and other artifacts. We used the relevant procedures to organize the section headings within each policy.
The organization maintains a contact list of everyone needed during a crisis. This includes security leads, legal counsel, and law enforcement. Security leads act as the primary point of contact and must be available every hour of every day. All employees and contractors must report any security weaknesses they notice immediately. To stay organized, the team uses a secure database to track every incident with a unique ID. This database stores logs and notes for at least five years to meet legal requirements.
The organization uses automated tools to watch for red flags 24/7. The incident response process starts the moment someone detects unusual activity. This includes incidents involving malware, a compromised account, missing laptop and data spillage. Security leads investigate every report to ensure the network stays safe.
The organization requires all outside partners and vendors to report security issues immediately. These partners receive contact information so they can alert us when they find a problem. This safety net includes both internal teams and external experts working together.
CMMC Objectives Covered in This Section:
The organization maintains an Incident Response Plan (IRP) for handling security crises. The CISO reviews and approves this plan every year. To keep the strategy safe from hackers, the team stores copies in a restricted digital vault. Once a team member confirms a real incident, they follow the response procedures. They record every detail in a central database and take action to contain and remove the threat.
A specialized team manages these response efforts. This group includes IT staff, executives, and department leaders affected by the breach. If needed, the organization brings in forensic experts and legal consultants to help. Incident response handlers sign and time stamp actions taken during the response. When collecting evidence, the team follows strict "chain of custody" rules. Staff work in pairs so one person can record events while the other performs technical fixes.
If sensitive data "spills", the team must act to move the information to a safe place. The team must sanitize the affected hardware. The organization maintains a Disaster Recovery Plan (DRP) to get systems back online. Leaders specify Recovery Time Objectives (RTOs) to define downtime tolerances. The DRP also specifies Recovery Point Objectives (RPOs) to define data backup frequencies. The team works with public relations experts to manage the company's reputation. The team tracks how fast they detect and stop threats to improve their defenses.
CMMC Objectives Covered in This Section:
The organization must follow specific government rules for reporting cyber attacks. Staff report incidents affecting the confidentiality of CUI to the Department of Defense. This report must go through the DIBNet portal within 72 hours of finding the problem. The organization maintains an External Certificate Authority (ECA) certificate at all times.
CMMC Objectives Covered in This Section:
The organization tests its disaster recovery plan every six months. During these tests, staff restore data and verify the system returns to normal. The team performs incident response drills every twelve months. These drills include a tabletop exercise where leaders practice making strategic decisions. Once a year, the team analyzes historical incident data, trends, and new threats. They use these findings to identify weaknesses in their current plans and training. The organization updates procedures based on these lessons. This cycle of testing and analysis ensures the company’s defenses grow more capable.
CMMC Objectives Covered in This Section:
The team reviews and updates the DRP every year or after major system changes. This plan identifies essential business functions for the team to focus on first. All backups sit in a separate location away from the main systems. This separation prevents an attack on the live network from spreading to the saved files. Security remains a priority even for stored data. The organization encrypts all backups using FIPS-validated cryptographic modules. If encryption is not possible, the team must use physical locks and security to protect the data.
CMMC Objectives Covered in This Section:
FedRAMP guidance on how to write a control implementation statement states the following:
Write your policies before you start drafting your security plan. K2 GRC shows you exactly how each part of your policy connects to your security goals.
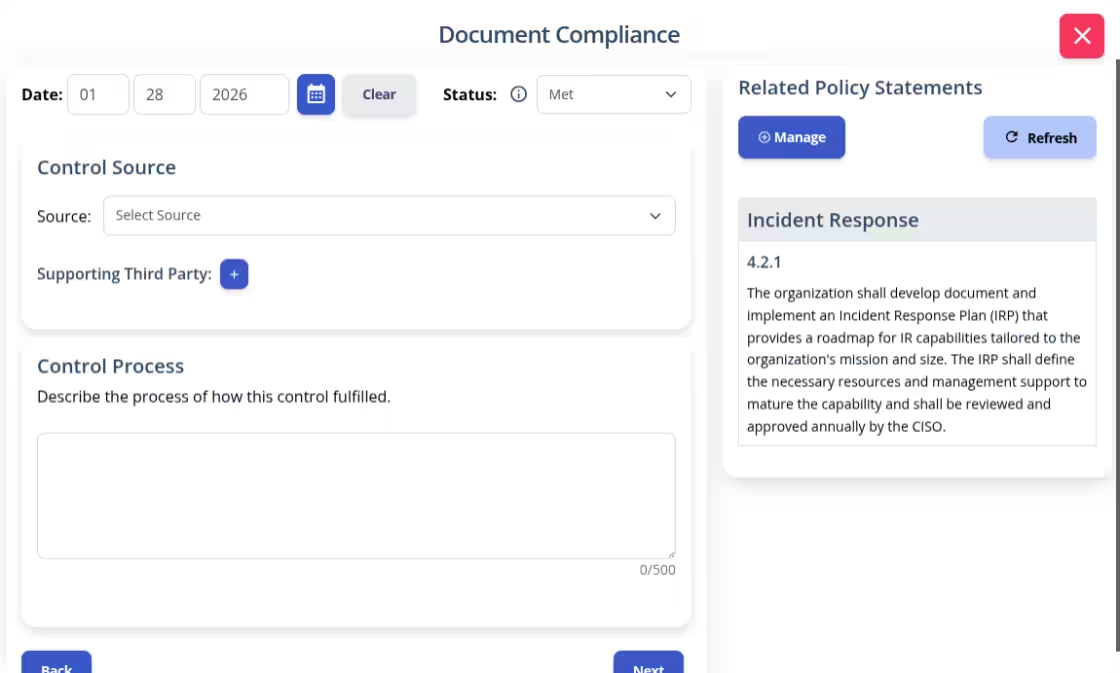
The input screen shows the specific policy rule and its ID number. This identifies relevant policy statements when writing your system security plan implementation statements. The system then adds your work to the final security plan template.
When a security incident hits, the clock is your biggest enemy. Every second of hesitation can mean more data lost and more damage to your reputation. It is a terrifying feeling to watch a "red flag" pop up and realize your team doesn't know who to call or what to do next. But you don't have to stay in that place of fear. By building a solid Incident Response plan, you take the power back. Confidence comes from knowing your backups are safe and your leaders are ready. This isn't about compliance, it's about protecting your business. Stop worrying about the "what-ifs" and start preparing for the "when." Download our Incident Response Policy template to get a professional, ready-to-use road map. Equip your team with the tools they need to stay calm, act fast, and stand strong, no matter what comes your way.