The Physical and Environmental Protection (PE) domain focuses on the system's physical space. Physical security keeps unauthorized people out of your non-public spaces. The controls build a boundary around your sensitive information. This means using badges, keys, or guards to ensure only authorized people can enter.
You must keep an eye on your physical space.
This includes using cameras or alarm systems to detect people entering restricted areas. You must track every guest who enters your building. Visitors must sign in, wear a badge, and stay with an escort at all times. Managing your environment protects you from "real world" accidents that software cannot fix. Strong locks and cameras make it very difficult for someone to walk off with a laptop or a server.
Visitor logs provide a history of exactly who was in the building during a security event. PE controls ensure that your data is safe in the physical world. It builds a secure home for your technology so that your digital defenses can do their job.
Domain level policies address the controls implemented within systems and organizations. Policies are the perfect home to define control parameters, such as frequencies. Procedures describe the implementation of policies or controls. Organizations may document procedures within the system security plan or within separate documents. Here are some of the principles that guided this physical and environmental protection policy:
A cover page tracks specific details regarding the policy, including:
NIST SP 800-53 defines specific objectives for domain-level policies. From this guidance we incorporate the following major sections into our policy:
The purpose statement should identify why the policy exists and what it aims to achieve.
The scope should identify who it applies to and under what circumstances.
The policy governance section covers most of the organization defined parameters. These subsections cover the following details:
The fourth section includes our policy statements. Subsection headings group related Policy statements together. Each policy statement has a unique number for traceability to other documents. A policy statement number consists of the section, subsection, and policy statement order.
The fifth section identifies the relevant roles and responsibilities identified in the policy. A single, short paragraph describes the responsibilities for each role. The sixth section identifies the supporting procedures. We opted to align our subsection headings with the names of supporting procedures. The seventh section identifies related documents, to include relevant policies. The eighth section documents a revision history. This table captures policy changes, including: version, effective date, approver(s), change summaries. The ninth section captures a formal authorization of the policy by the policy owner.
NIST identified a named set of procedures for each practice within NIST SP 800-171. The assessment guide (SP 800-171A) contains the original mappings. The CMMC assessment guides include this mapping as well. The potential assessment methods and objects section contains a subsection called examine. Within each practice, NIST identified relevant policies, procedures and other artifacts. We used the relevant procedures to organize the section headings within each policy.

Non-public spaces within the organization’s facilities shall be defined and segmented based on security requirements. Access control mechanisms shall restrict access to non-public spaces to credentialed individuals. Physical access to sensitive operating environments (e.g., server rooms, network closets) is further restricted to only those authorized personnel with a specific functional need for access.
The identification and authorization of personnel permitted to access non-public spaces are managed in accordance with the Access Control Policy. Authorization is based on a formal access request process that includes background checks and a documented business need. In alignment with the quarterly access review defined in the AC policy, the Master Physical Access List (including keys and badges) shall be audited to ensure physical access remains restricted to currently authorized personnel.
All visitors must be escorted by an authorized employee at all times while within non-public areas. Visitor access records, including manual logs and digital sign-in data, shall be maintained for a period of three (3) years.
The Security Officer or Facility Manager shall review visitor access records monthly to identify discrepancies or unauthorized access patterns. Any anomalies, such as unescorted entries or failures to sign out, shall be reported immediately to the CISO and documented as a potential security incident.
Detailed audit logs that track individuals accessing non-public spaces are maintained. Individuals must sign a manual log when accessing non-public spaces not secured with an automated badge system.
An inventory of physical access devices (keys, badges, tokens) shall be maintained. Unissued devices must be physically secured. Locks and access codes are changed immediately in response to lost keys or terminated employees.
CMMC Objectives Covered in This Section:
The physical facility shall be protected and monitored using intrusion detection systems and/or video surveillance to detect and record unauthorized physical access incidents.
Video surveillance footage and intrusion detection logs shall be reviewed by IT or Security personnel on a monthly basis or in response to a suspected security incident. Records of these reviews shall be maintained to demonstrate ongoing monitoring. The physical recording equipment and monitoring consoles shall be secured in restricted-access areas to prevent unauthorized tampering or deletion of audit data.
The support infrastructure for organizational systems (including power, temperature, and humidity) shall be continuously monitored to ensure operating environments remain within vendor-specified tolerances. Alerts for environmental anomalies shall be automatically generated and sent to designated personnel.
CMMC Objectives Covered in This Section:
Managers shall ensure that shared output devices, including printers, copiers, and facsimile machines, are located in secured areas or locations actively monitored by personnel to prevent the unauthorized retrieval of hard-copy records.
For any output devices authorized to process Controlled Unclassified Information (CUI), the organization shall implement "Follow-Me Printing," "Secure Print," or an equivalent identity-based release mechanism. This requires the authorized user to physically authenticate at the device (e.g., via badge swipe or PIN) before the print job is released, ensuring the user is present to take immediate custody of the hard-copy records.
Users are responsible for immediately marking hard-copy records with the appropriate CUI designation upon collection and ensuring they are not left unattended.
CMMC Objectives Covered in This Section:
Physical access to systems for the purpose of performing hardware changes or maintenance is restricted to authorized personnel defined in the Access Control Policy. These restrictions are enforced through the use of locked server racks, badge-access controlled server rooms, and/or physical tamper-evident seals.
All physical access associated with system changes shall be defined and documented within the Change Management process (e.g., via a visitor log or a specific change ticket entry).
Physical access for these activities must be approved by the Security Officer or System Administrator prior to entry.
Physical access points to the network infrastructure, including patch panels and wall jacks in public areas, shall be visually inspected quarterly for unauthorized modifications. Access points located within restricted operating environments shall be inspected quarterly. All inspections shall be documented in the Physical Security Audit Log, noting the date, the specific locations inspected, and the presence or absence of tampering.
CMMC Objectives Covered in This Section:
FedRAMP guidance on how to write a control implementation statement states the following:
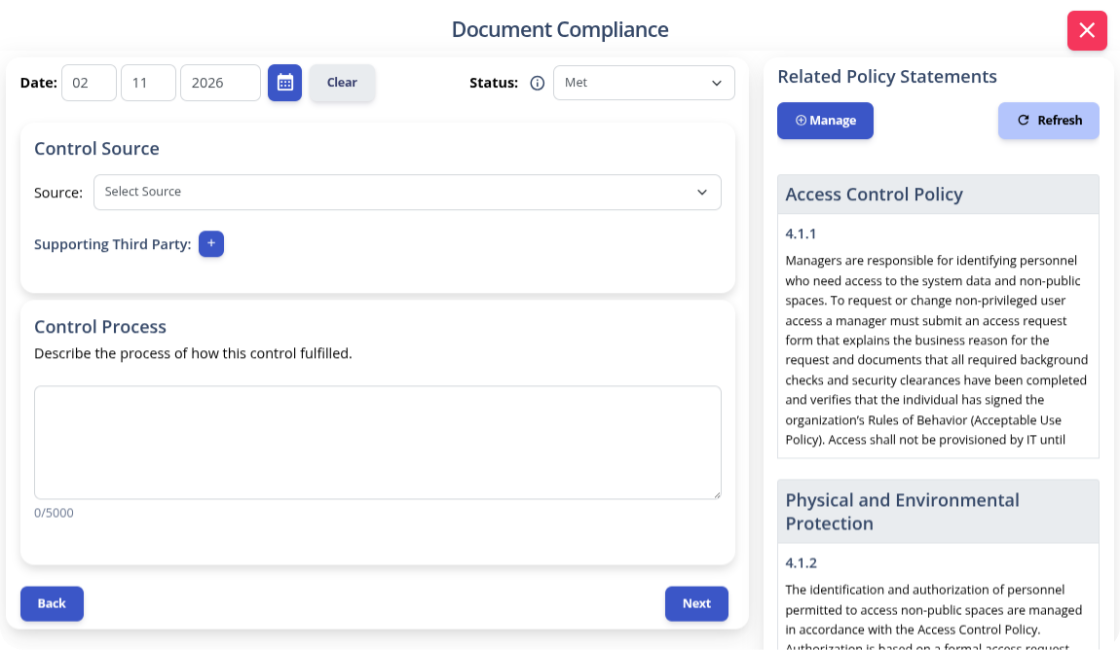
Write your policies before you start drafting your security plan. K2 GRC shows you exactly how each part of your policy connects to your security goals. This starts with selecting an objective to document.
.png)
After selecting a criteria, K2 GRC shows policy statements relevant to that criteria. The input screen shows the specific policy name and the statement’s number. This enables users to cite relevant policy sections within the control narratives. The system aggregates these control narratives to populate the system security plan (SSP).
It's terrifying that someone can bypass technical controls by accessing an unlocked room. You have worked too hard to let an unescorted visitor put your entire mission at risk.
You deserve the peace of mind that comes from knowing your physical space is as secure as your network. Having a Physical and Environmental Protection policy takes the guesswork out of security. You stop wondering who has a spare key.
Instead, you can create a culture of vigilance. A culture that protects your equipment, data, and reputation. Don't spend your time struggling to write CMMC policies from scratch. Download our pre-written and pre-mapped Physical and Environmental Protection Policy template today.
Give your team the roadmap they need to secure your facility. Secure your data’s home today so you can focus on growing your business tomorrow.