The Personnel Security (PS) domain focuses on people who work for your organization. The individuals who use your systems are often the biggest risk to your security. This domain ensures you hire trustworthy individuals and manage their access over time. You must perform background checks on individuals before granting them system access. When someone quits or changes roles, update their system access based on this change.
This may include disabling their accounts and collecting their keys, badges, and technology. Managing your people protects against insider threats that firewalls cannot stop. Clear off-boarding checklists ensure that no accounts remain active for former employees. Personnel security transforms your team from a risk to a strong line of defense.
Domain level policies address the controls implemented within systems and organizations. Policies are the perfect home to define control parameters, such as frequencies. Procedures describe the implementation of policies or controls. Organizations may document procedures within the system security plan or within separate documents. Here are some of the principles that guided this personnel security policy:
A cover page tracks specific details regarding the policy, including:
NIST SP 800-53 defines specific objectives for domain-level policies. From this guidance we incorporate the following major sections into our policy:
The purpose statement should identify why the policy exists and what it aims to achieve.
The scope should identify who it applies to and under what circumstances.
The policy governance section covers most of the organization defined parameters. These subsections cover the following details:
The fourth section includes our policy statements. Subsection headings group related Policy statements together. Each policy statement has a unique number for traceability to other documents. A policy statement number consists of the section, subsection, and policy statement order.
The fifth section identifies the relevant roles and responsibilities identified in the policy. A single, short paragraph describes the responsibilities for each role. The sixth section identifies the supporting procedures. We opted to align our subsection headings with the names of supporting procedures. The seventh section identifies related documents, to include relevant policies. The eighth section documents a revision history. This table captures policy changes, including: version, effective date, approver(s), change summaries. The ninth section captures a formal authorization of the policy by the policy owner.
NIST identified a named set of procedures for each practice within NIST SP 800-171. The assessment guide (SP 800-171A) contains the original mappings. The CMMC assessment guides include this mapping as well. The potential assessment methods and objects section contains a subsection called examine. Within each practice, NIST identified relevant policies, procedures and other artifacts. We used the relevant procedures to organize the section headings within each policy.
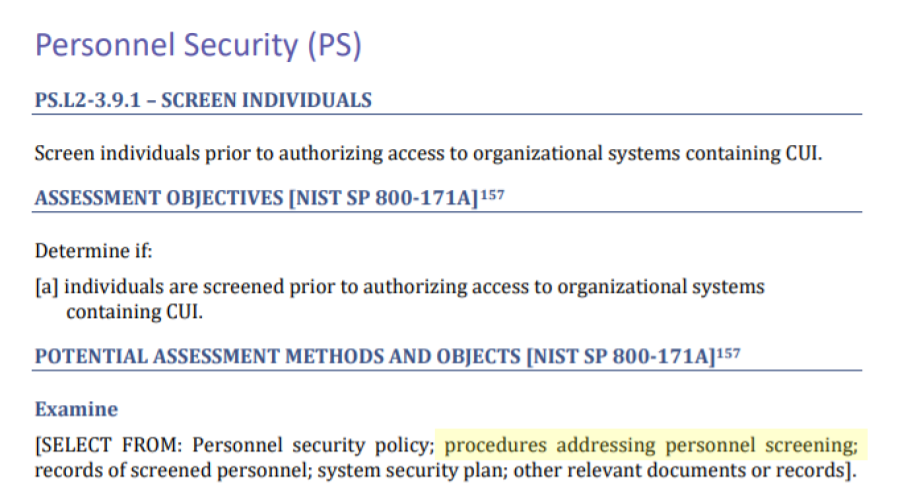
All individuals must pass a background check before they receive system access. This screening must reveal no major findings. Major findings include felony convictions for fraud, theft, or any crime involving data. The depth of the background check should match the level of risk and sensitivity of the role. The organization re-evaluates screenings every five years. Screenings are also required when a new role assignment increases an individual's responsibilities.
CMMC Objectives Covered in This Section:
When an employee leaves or changes jobs, dedicated personnel must manage the risk. The team must revoke access immediately in response to terminations with cause. For voluntary departures, the team must revoke access within 24 hours. Access revocations include facility access and information system access.
The organization uses a formal off-boarding checklist. Personnel must return all company property before they walk out the door. This includes laptops, media, mobile phones, office keys, and ID badges. Assigned personnel must verify the disablement of digital accounts in the system. They must also collect all physical documents and corporate credit cards.
If an employee moves to a new role, dedicated personnel right-size their access. The employee must return any tools or keys they no longer need for their new job. The team then revokes any permissions to sensitive data that belonged to the old role. This ensures individuals only have access they need to perform their current duties.
CMMC Objectives Covered in This Section:
Dedicated personnel maintain a Compliance Matrix of signed access agreements. The organization audits this matrix every quarter. Personnel with system access must sign an agreement every 12 months to stay valid. If an account does not have a current agreement on file, it fails the audit. This process ensures that every user has agreed to follow the company security rules.
CMMC Objectives Covered in This Section:
The organization requires all external providers to follow the same security rules. Official contracts or service agreements must contain these written rules. Providers must prove their identity and show they have passed a background check. They are also required to tell the organization about any staff changes within 24 hours. The organization reviews external provider third-party audit reports once a year. This review verifies that the provider is performing background checks and security training.
CMMC Objectives Covered in This Section:
FedRAMP guidance on how to write a control implementation statement states the following:
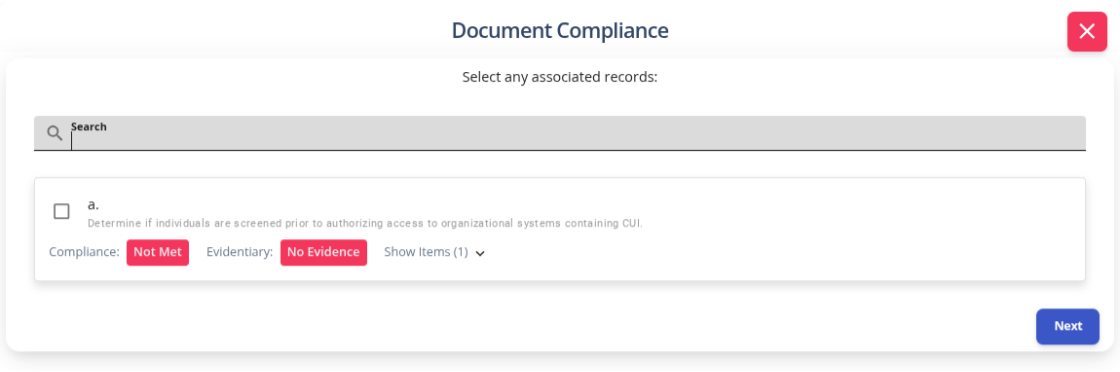
Write your policies before you start drafting your security plan. K2 GRC shows you exactly how each part of your policy connects to your security goals. This starts with selecting an objective to document.
After selecting a criteria, K2 GRC shows policy statements relevant to that criteria. The input screen shows the specific policy name and the statement’s number. This enables users to cite relevant policy sections within the control narratives. The system aggregates these control narratives to populate the system security plan (SSP).
Your employees are your greatest asset, but they can also be your biggest source of worry. It is a heavy burden to wonder if a disgruntled former staff member still has a key to your digital front door. You want to trust your team completely, but in the world of security, you must also verify that trust. Without a formal plan for your people, you are leaving your company's future to chance. A solid Personnel Security policy gives you the confidence to lead without fear. It replaces that uneasy feeling in your gut with defined processes.
These processes include screening, managing, and off-boarding every person who touches your data. When you have a professional system in place, you protect your business from the inside out. You ensure that every person on your team is a vetted defender, not a hidden risk to your reputation. Don't wait for a hiring mistake or a messy departure to realize your rules are unclear. Download our Personnel Security Policy template today. Give your organization the professional foundation it deserves. Turn your workforce into your strongest shield and gain the peace of mind from a secure culture.